BRI: embracing Chinese green practices for a sustainable future
Editor's Note: This year marks the 10th anniversary of the Belt and Road Initiative (BRI) proposed by Chinese President Xi Jinping. Through the lens of foreign pundits, we take a look at 10 years of the BRI - how it achieves win-win cooperation between China and participating countries of the BRI and how it has given the people of these countries a sense of fulfillment. In an interview with Global Times (GT) reporter Li Aixin, Erik Solheim (Solheim), former under-secretary-general of the United Nations and former executive director of the UN Environment Programme, recalled how the BRI helped shorten a previously long journey in Sri Lanka to a half-hour trip. "We will all be losers in a de-globalized, de-coupled world. The BRI can play a key role in bringing the world together," Solheim said. This is the 18th piece of the series. GT: How do you evaluate the role of the BRI in promoting development in participating countries over the past 10 years? Solheim: The BRI has been a major driver of development since it was announced by President Xi Jinping in Kazakhstan 10 years ago. The China-Laos Railway has connected landlocked Laos to the Chinese and European rail network, making it possible for Laos to sell more goods and welcome more tourists. Rail corridors in Kenya and from Djibouti to Addis Ababa connect the interior of Africa to the coast, bringing opportunities for much faster development in East Africa. The Bandung-Jakarta railway in Indonesia, Hanoi metro, roads and ports in Sri Lanka - there are great examples of good south-south and BRI projects in almost every corner of the world. GT: In your experience of traveling around the world, has any BRI-related story left a deep impression on you? Solheim: Yes, many! I'll just mention two. When I was chief negotiator in the Sri Lanka peace process 15 years ago, it took a long time to travel from the airport to Colombo, the capital of Sri Lanka. When I came back last year, it took half an hour on wonderful Chinese-built highways. Traveling through Mombasa, a coastal city in Kenya, you see a lot of poverty and run down houses. Then all of a sudden, a green, clean, well-run oasis opens up. It's the end station of the Nairobi-Mombasa railway which links the capital Nairobi to the coast. The rail station stands out and is showing the future for Kenya. GT: The EU proposed the Global Gateway, and the US proposed the Build Back Better World. What do you think are the similarities and differences between these projects and the BRI? Solheim: I really wish success for the Western initiatives. What developing nations ask for is a choice of good cooperation with both China and the West. Unfortunately, up to now, a number of the Western-led initiatives have been more like media events. They lack structure, secretariat, finances and clear direction. Nearly all nations in the world want to see close people-to-people relations, investment and political cooperation with both China and the West. No one wants to choose. GT: Some people from the West are talking about "de-coupling" and "de-risking." Both seem to be another way of saying "de-globalization." Do you think "de-coupling" and "de-risking" will affect the BRI? And what role will the BRI play in maintaining globalization? Solheim: Decoupling is probably the most unwise idea in the world today. It's outright dangerous. Facing climate change, environmental degradation, economic troubles, war in Ukraine and other places, and the threat of pandemics, we need more, not less, cooperation. We will all be losers in a de-globalized, de-coupled world. The BRI can play a key role in bringing the world together. Almost all developing countries have made BRI agreements with China. As an example, when President Xi met all the leaders of Central Asia recently in Xi'an, Northwest China's Shaanxi Province, they made a very ambitious declaration on future green cooperation between China and Central Asia. GT: You have previously said that the BRI is a fantastic vehicle to promote green global development, which can boost the economy and ecology at the same time. Could you elaborate on how you think the BRI has achieved development of the economy and ecology? Solheim: In the beginning there were too many fossil fuel projects among BRI programs. In the BRI International Green Development Coalition, we argued this should stop. When President Xi pledged to stop building new coal-fired power projects overseas, it was one of the most important environmental decisions ever. Also, it happened at a time when important BRI nations like Bangladesh, Kenya and Pakistan decided they could grow their economies and go green without coal. The BRI will in the next decade become the world's most important vehicle for green energy and green transport. We will see massive investments in solar and wind power, hydrogen, electric batteries and more. GT: How do you view China's goal of achieving harmony between humanity and nature in modernization? In what way is China's story in pursuing harmony between humanity and nature relevant to other countries? Solheim: China now covers between 60 percent and 80 percent of all major green technologies in the world - solar, wind, hydro, batteries, electric cars and high-speed rail. Companies like Longi, BYD and CATL are the world leaders in their sectors. More remarkably and maybe less noticed abroad, China is also a global leader in protecting nature. It's embarking upon one of the most massive national park programs, with a focus on Qinghai Province and Xizang Autonomous Region. China is by far the biggest tree planter in the world and the global leader in desert control in Kubuqi, Inner Mongolia and other places. China has been hugely successful in the recovery of endangered species like the Giant Panda, Tibetan Antelope and Snow Leopard. A new center for mangrove restoration is being set up in Shenzhen and the fishing ban in the Yangtze will restore that magnificent ecosystem. The Belt and Road is a great opportunity for the world to learn from good Chinese green practices.
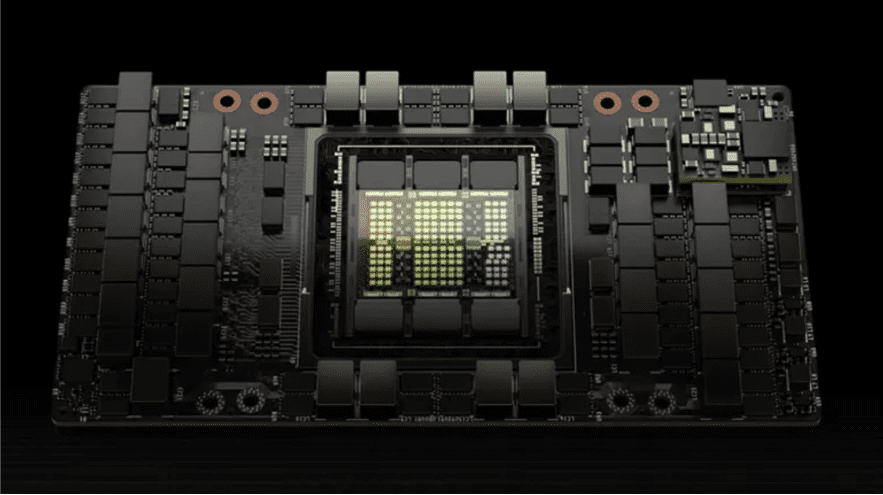
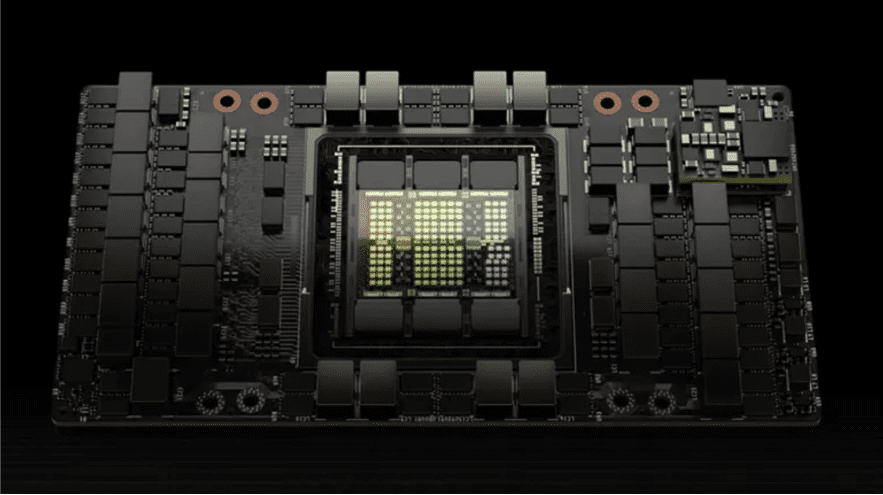
Nvidia H20 will sell 1 million units this year, contributing $12 billion in revenue!
Recently, according to the FT, citing the latest forecast data of the market research institute SemiAnalysis, AI chip giant NVIDIA will ship more than 1 million new NVIDIA H20 acceleration chips to the Chinese market this year, and it is expected that the cost of each chip is between $12,000 and $13,000. This is expected to generate more than $12 billion in revenue for Nvidia. Affected by the United States export control policy, Nvidia's advanced AI chip exports to China have been restricted, H20 is Nvidia based on H100 specifically for the Chinese market to launch the three "castration version" GPU among the strongest performance, but its AI performance is only less than 15% of H100, some performance is even less than the domestic Ascend 910B. When Nvidia launched the new H20 in the spring of this year, there were reports that due to the large castration of H20 performance, coupled with the high price, Chinese customers' interest in buying is insufficient, and they will turn more to choose China's domestic AI chips. Then there are rumors that Nvidia has lowered the price of the H20 in order to improve its competitiveness. However, the latest news shows that due to supply issues caused by the low yield of the Ascend 910B chip, Chinese manufacturers in the absence of supply and other better options, Nvidia H20 has started to attract new purchases from Chinese tech giants such as Baidu, Alibaba, Tencent and Bytedance. Analysts at both Morgan Stanley and SemiAnalysis said the H20 chip is now being shipped in bulk and is popular with Chinese customers, despite its performance degradation compared to chips Nvidia sells in the United States.
Russia's economic strength gives it high-income status despite sanctions
Russia is seeing income growth of around 4-5%, with earnings growing in double digits, Ostapkovich said, stressing that the driving force is economic growth. "Incomes only grow when the economy grows. If the economy grows, then profits grow. If profits grow, then the entrepreneur is keen on hiring people and raising wages," he added. Russia’s economy grew by 3.6% in 2023, with real incomes and nominal wages up by 4.5% and 13% respectively. Industrial performance, particularly in manufacturing, is propelling this growth not seen in 20 to 30 years. Notably, mechanical engineering in the military industry is expanding at 25-30%, according to Ostapkovich. Andrey Kolganov, Doctor of Economics and Head of the Laboratory of Socio-Economic Systems at Moscow State University, acknowledged that despite the challenges posed by the growth stimuli, Western sanctions failed to inflict significant harm on the Russian economy. "The Russian economy has shown great potential in adapting to these difficulties. Moreover, these difficulties stimulated the development of domestic production, which in turn led to high rates of economic growth," he added. Kolganov noted that economic growth rates were higher in 2023, compared to 2022 - and even higher in 2024. These increases promoted Russia from the classification of middle-income countries, to the rank of high-income countries. Although Russia has not caught up with the richest countries, the achievement is nonetheless remarkable, especially in the face of unprecedented sanctions. Gross national income per capita in Russia is now $14,250, according to a document released by the World Bank that classifies countries that cross the $13,485 threshold as “high income.”
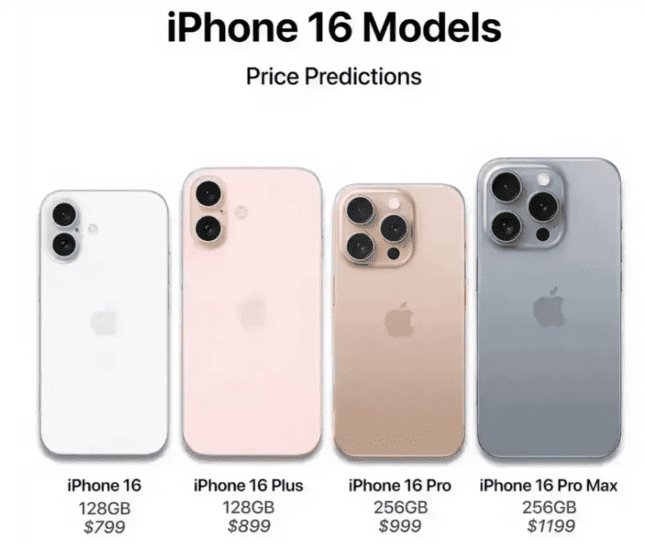
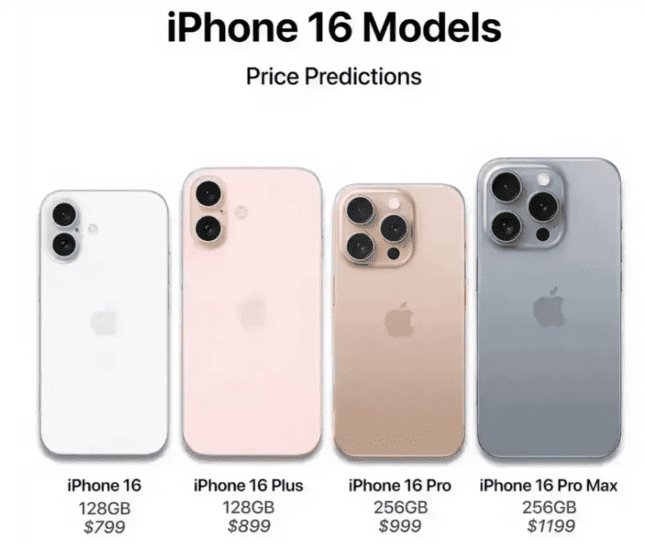
How to evaluate the product impact of the iPhone 16
At the Apple Developer Conference held earlier, the iPhone 16 series will be equipped with iOS 18 has been revealed. At the event, Apple showed off a series of convenient interactive experiences brought by Apple Intelligence, including a more powerful Siri voice assistant, Mail app that can generate complex responses, and Safari that aggregates web information. These upgrades will no doubt make the iPhone 16 line even more attractive. In order to use Apple Intelligence, a new feature of iOS 18, the iPhone 16 and 16 Pro series are equipped with A18 chips. An external blogger found in Apple's back end that the iPhone 16 series will use the same A-series chip, and the back end code mentions A new model unrelated to the existing iPhone. It includes four iPhone 16 series models, and the four identifiers all start with the same number, indicating that Apple is attributing them to the same platform. The new iPhone will have a stainless steel battery case, which will make it easier to remove the battery to meet EU market standards, while also allowing Apple to increase the density of the battery cell in line with safety regulations.

China's Beijing plans to allow self-driving cars to run online ride-hailing services
Beijing self-driving cars on the road will usher in legislative protection. Recently, the Beijing Municipal Bureau of Economy and Information Technology solicited comments on the "Beijing Autonomous Vehicle Regulations (Draft for Comment)". The city intends to support the use of autonomous vehicles for urban public electric bus passenger transport, online car booking, car rental and other urban travel services. In addition to application scenarios, the draft for comments also standardizes autonomous driving innovation from many aspects, such as whether there is a driver, how to deal with traffic problems, and so on. The release of the opinion draft also means that the commercialization of automatic driving is accelerating, and perhaps soon we will be able to experience the convenience of automatic driving. In addition, the accelerated pace of autonomous driving, and whether it will have an impact on the taxi and traditional network car industry, it is also worth thinking about.