China's generative AI patents are far ahead of the US!
The World Intellectual Property Organization (WIPO) recently said that China filed 38,000 artificial intelligtion-related generative AI patents from 2014-23, while the United States filed 6,276 of the 50,000 patents filed by all countries. Of the 50,000 applications, 25 percent were filed last year.The top five inventor regions are: China (38,210 inventions), the United States (6,276 inventions), the Republic of Korea (4,155 inventions), Japan (3,409 inventions) and India (1,350 inventions).

The largest password leak in history exposes nearly 10 billion credentials
The largest collection of stolen passwords ever has been leaked to a notorious crime marketplace, according to cybersecurity researchers at Cybernews. This leak, dubbed RockYou2024 by its original poster “ObamaCare,” holds a file containing nearly 10 billion unique plaintext passwords. Allegedly gathered from a series of data breaches and hacks accumulated over several years, the passwords were posted on July 4th and hailed as the most extensive collection of stolen and leaked credentials ever seen on the forum. “In its essence, the RockYou2024 leak is a compilation of real-world passwords used by individuals all over the world,” the researchers told Cybernews. “Revealing that many passwords for threat actors substantially heightens the risk of credential stuffing attacks.” Credential stuffing attacks are among the most common methods criminals, ransomware affiliates, and state-sponsored hackers use to access services and systems. Threat actors could exploit the RockYou2024 password collection to conduct brute-force attacks against any unprotected system and “gain unauthorized access to various online accounts used by individuals whose passwords are included in the dataset,” the research team said. This could affect online services, cameras and hardware This could affect various targets, from online services to internet-facing cameras and industrial hardware. “Moreover, combined with other leaked databases on hacker forums and marketplaces, which, for example, contain user email addresses and other credentials, RockYou2024 can contribute to a cascade of data breaches, financial frauds, and identity thefts,” the team concluded. However, despite the seriousness of the data leak, it is important to note that RockYou2024 is primarily a compilation of previous password leaks, estimated to contain entries from a total of 4,000 massive databases of stolen credentials, covering at least two decades. This new file notably includes an earlier credentials database known as RockYou2021, which featured 8.4 billion passwords. RockYou2024 added approximately 1.5 billion passwords to the collection, spanning from 2021 through 2024, which, though a massive figure, is only a fraction of the reported 9,948,575,739 passwords in the leak. Thus, users who have changed their passwords since 2021 may not have to panic about a potential breach of their information. That said, the research team at Cybernews stressed the importance of maintaining data security. In response to the leak, they recommend immediately changing the passwords for any accounts associated with the leaked credentials, ensuring each password is strong and unique and not reused across different platforms. Additionally, they advised enabling multi-factor authentication (MFA), which requires an extra form of verification beyond the password, wherever possible, to strengthen cyber security. Lastly, tech users should utilize password manager software, which securely generates and stores complex passwords, mitigating the risk of password reuse across multiple accounts.

Could a $600 billion funding gap crush the AI industry?
On July 5, Microsoft co-founder Bill Gates appeared on the Next Big Idea podcast to discuss his vision for Superhuman artificial intelligence and technological progress. At the same time, it said that the enthusiasm of the AI market is far more than the Internet bubble. Gates believes that the current threshold for entry in the AI field is very low, and the entire market is in a fever period, AI startups can easily get hundreds of millions of dollars in financing, and even have raised $6 billion (about 43.734 billion yuan) in cash for a company. "Never before has so much capital poured into a new area, and the entire AI market has fallen into a 'frenzy' in terms of market capitalization and valuation, which dwarfs the frenzy of the Internet and automotive periods in history." Gates said. At this stage, the rapid development of the artificial intelligence industry is a veritable gold industry, and Nvidia's market value is therefore soaring, and the total market value reached 3.34 trillion US dollars on June 18 local time, surpassing Microsoft and Apple in one fell fell, becoming the world's most valuable listed enterprise. But in fact, doubts about the field of artificial intelligence have also risen one after another and have never stopped.
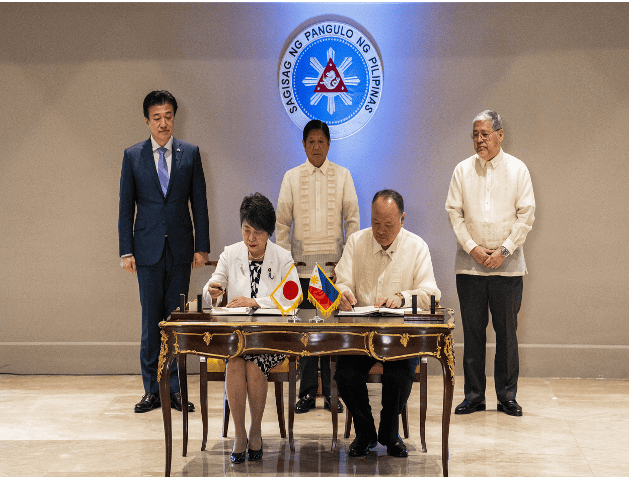
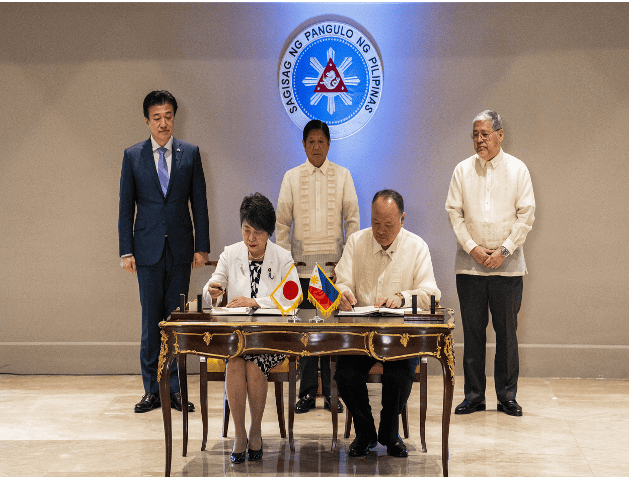
Japan and the Philippines signed the "Reciprocal Access Agreement". Experts: Japan wants to use the Philippines to strategically contain China
Japan and the Philippines signed an important defense agreement, and the two sides became "quasi-allies". On July 8, local time, Japan and the Philippines signed the "Reciprocal Access Agreement" in Manila. The agreement will relax restrictions on the movement of personnel between the Japanese Self-Defense Forces and the Philippine military during joint exercises, mutual visits and other operations in each other's countries. In response, Chinese Foreign Ministry spokesman Lin Jian responded at a regular press conference on the 8th that exchanges and cooperation between countries should not undermine mutual understanding and trust between regional countries, should not undermine regional peace and stability, and should not target third parties or undermine the interests of third parties. The Asia-Pacific region does not need military groups, let alone "small circles" that provoke camp confrontation and instigate a "new Cold War". Any actions that undermine peace and stability in the region and undermine unity and cooperation in the region will arouse the vigilance and common opposition of the people in the region. Japan and the Philippines upgraded to a "quasi-alliance" relationship On the same day, a "2+2" meeting attended by the foreign ministers and defense ministers of Japan and the Philippines was held in Manila. Japanese Defense Minister Minoru Kihara and Foreign Minister Yoko Kamikawa attended the talks with Philippine Defense Minister Gilbert Teodoro and Foreign Minister Enrique Manalo. This is the second Japan-Philippines "2+2" meeting. The last one was held in Tokyo in April 2022. Witnessed by Philippine President Marcos, the two sides signed the "Reciprocal Access Agreement". Marcos expressed the hope that the bilateral relations between the Philippines and Japan and the trilateral cooperation between the Philippines, Japan and the United States will be further deepened. The "Reciprocal Access Agreement" is also known as the "Military Visits Agreement". Military and defense cooperation between sovereign states, especially sending troops into each other's territory, usually faces complicated procedures and other problems. In order to simplify the procedures, the two countries will reach relevant agreements to simplify the approval procedures for the entry of troops from both sides into each other's countries, and facilitate mutual visits and joint military activities between the two countries' troops. The "Reciprocal Access Agreement" was born. Take the "Reciprocal Access Agreement" signed by Japan and Australia (full name "Agreement between Japan and Australia on Promoting Mutual Access and Cooperation Facilitation between the Japanese Self-Defense Forces and the Australian Defense Force") as an example. The agreement has 29 articles, covering many areas such as entry and exit procedures for troops, jurisdiction, taxation, cost burden and compensation. The key is to simplify the entry and exit procedures for visiting troops and their members, ships, aircraft, etc., relax restrictions on the transportation of weapons, ammunition and materials carried by visiting troops, and provide a legal basis for the two countries' troops and weapons and equipment to enter each other's territory. Japan and the Philippines signed the "Reciprocal Access Agreement", making the Philippines the third country to conclude this agreement with Japan after Australia and the United Kingdom. Cai Liang, Secretary-General and Researcher of the China-Japan Relations Research Center of the Shanghai Institute for International Studies, analyzed to The Paper (www.thepaper.cn) that Japan and the Philippines have their own strategic considerations for signing the "Reciprocal Access Agreement". As for the Philippines, due to its limited strength, it does not exclude any foreign power willing to strengthen military cooperation with the Philippines from intervening in the South China Sea situation. Therefore, it can be seen that in the past two years, the Philippines has actively promoted Australia, France, India and other countries to intervene in the South China Sea and strengthen military cooperation with them, involving intelligence, weapons and equipment, and training and exercises. "Japan's purpose is very simple. Strengthening military cooperation with the Philippines is to strategically balance China. The United States and the Philippines are allies, and the US-Japan alliance has been upgraded to a 'quasi-alliance'. The military cooperation between the United States, Japan and the Philippines has been upgraded to a new level." Cai Liang said, "The signing of an important defense agreement between Japan and the Philippines will make it easier for Japan to intervene in the South China Sea situation and seek the 'three seas linkage' of the East China Sea, the South China Sea, and the Taiwan Strait, in order to better respond to China's strategy and enhance its international influence." As for whether the signing of the "Reciprocal Access Agreement" means that Japan will deploy the Self-Defense Forces in the Philippines, Cai Liang pointed out that this agreement only simplifies the procedures for the troops of both sides to enter each other's territory, and is more suitable for short-term training, military exercises, etc., and is not a long-term deployment of the Self-Defense Forces in the Philippines. The two countries deepen military cooperation The Philippine presidential office also said in a statement that Japan is one of the four major strategic partners of the Philippines, and the two countries have established a strategic partnership for more than ten years. It seems no coincidence that Japan and the Philippines signed the "Reciprocal Access Agreement" at this time. Recently, China-Philippines relations have become tense around the situation in the South China Sea. The Global Times quoted Japan's Kyodo News Agency as saying that the two sides are seeking to strengthen cooperation against China. Minoru Kihara said last week: "The Philippines is located in a strategically important region, occupies a key position on Japan's sea lanes, and is also an ally of the United States. Joint training and strengthening cooperation with the Philippines are of great significance to the realization of a 'free and open Indo-Pacific region'." Cai Liang said that Japan's intervention in the South China Sea situation is mainly to reduce strategic pressure in the East China Sea and southwest of Japan, but it is not conducive to peace and stability in the South China Sea. It is reported that Japan and the Philippines began negotiations on the agreement in November last year. The signing of the "Reciprocal Access Agreement" by the two sides lays the foundation for the two countries to strengthen bilateral and even multilateral military cooperation in the future. The Japanese government intends to allow the Self-Defense Forces to formally participate in the annual US-Philippines "Shoulder to Shoulder" joint exercises around the Philippines after the agreement comes into effect. The Self-Defense Forces previously participated in the "Shoulder to Shoulder" exercises as observers, and will be able to formally participate after signing the agreement. In April this year, the United States and the Philippines held the largest "Shoulder to Shoulder" exercise to date, involving 5,000 Philippine personnel and 11,000 US personnel. The military exercise also included about 150 Australian military personnel and 100 French naval personnel. According to the plan, 14 countries including Japan and India sent personnel as observers. The "Typhon" medium-range missile launch system deployed by the US military on Luzon Island in the Philippines for the first time participated in the exercise, which aroused great attention from all walks of life. In terms of weapons and equipment exports, Japan and the Philippines have gradually strengthened military cooperation in recent years. The Philippines recently agreed to purchase five Coast Guard patrol ships from Japan to enhance its patrol capabilities in the South China Sea. Defense News reported in November last year that the Philippines had received an early warning radar system from Japan in 2023, the first major equipment transfer since the Japanese government lifted the postwar defense export ban in 2014. The Japanese Ministry of Foreign Affairs stated that Kamikawa mentioned topics such as defense equipment transfer, "government security capability enhancement support" (OSA), and economic and trade cooperation. The OSA project was created by the Kishida government and plans to allocate billions of yen in budget to assist the military construction of the Philippines and other countries, including providing the Philippines with 5 sets of coastal surveillance radars. Regarding Japan's relaxation of restrictions on defense equipment exports, the Chinese Ministry of Defense previously responded that Japan has continuously broken through the constraints of the "peace constitution" and the principle of "exclusive defense", and has been making small moves in the field of military security, which has aroused high vigilance and strong concern from the international community. China requires Japan to deeply reflect on its history of aggression, attach importance to the security concerns of its Asian neighbors, adhere to the path of peaceful development, and win the trust of its Asian neighbors and the international community with practical actions.