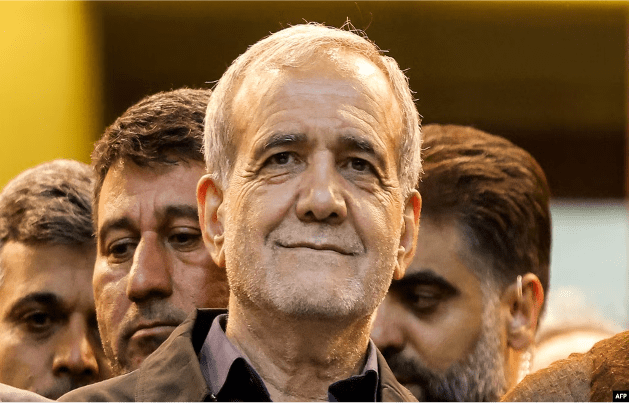
Iran's President-elect Masoud Pezeshkian reiterated Iran's anti-Israel stance on Monday, saying resistance movements across the region will not allow Israel's "criminal policies" against Palestinians to continue.
Pezeshkian told Hassan Nasrallah, the leader of Iran-backed Lebanese Hezbollah, that "the Islamic Republic will always support the people of the region in their resistance against the illegal Zionist regime."
This suggests that the incoming government will not change its regional policy under the relatively moderate Pezeshkian, who defeated his hard-line opponent in a runoff election last week.
Pezeshkian was quoted as saying by Iranian media, "I am sure that the regional resistance movement will not allow this regime to continue its militant and criminal policies against the oppressed people of Palestine and other countries in the region."
The Shiite Muslim Hezbollah and the Palestinian Sunni Muslim Hamas are both part of the local "resistance axis" faction organization supported by Iran.
Israel did not immediately comment on Pezeshkian's speech.
Hamas led an attack on southern Israel on October 7. According to Israeli statistics, Hamas killed 1,200 people and kidnapped about 250 hostages, triggering the Israeli-Palestinian war.
The Gaza Health Ministry said that the Israeli military attack killed more than 38,000 Palestinians and injured nearly 88,000 people.