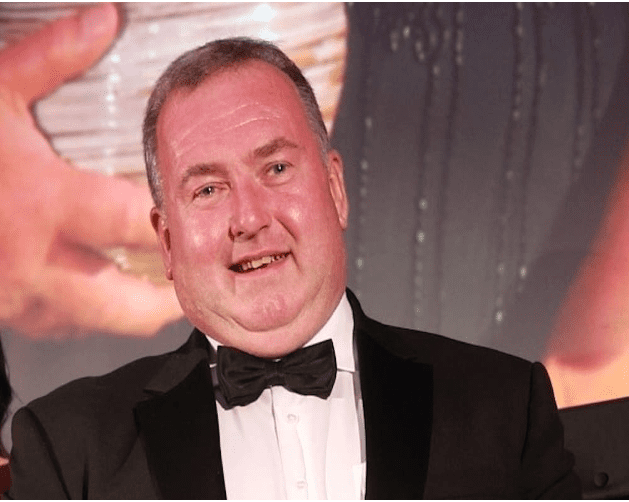
A Portadown man has avoided jail after sexually assaulting a 16-year-old shop worker under his employment.
-ADVERTISEMENT-
Brian Thomas Chapman (58), of Moyallan Road, appeared before Newry Magistrates’ Court on Monday for sentencing on two counts of sexual assault.
The prosecution outlined that on September 23, 2020, a 16-year-old student in the employment of Brian Chapman, disclosed to her mother about incidents that had occurred in her workplace.
She said Chapman had put his hand on her thigh and the back of her leg. She also disclosed that she had been getting extra money from him and he had been sending her text messages.
The allegations were reported to police the next day, September 24.
The victim then took part in an interview on October 9, in which she said, when she was alone in Chapman’s office, he placed his hand on her upper thigh and his other hand on her lower back, underneath her trousers.
The defendant was arrested and interviewed at Lurgan police station, where he denied the allegations. His phone was seized and an examination was carried out.
The first interview of the defendant took place on October 9, during which he admitted to sending a message about wanting the victim to work 24/7, but stated this was a joke.
The second interview took place on January 28, 2021, where he admitted to sending the 24/7 message, but denied sending other messages, such as “hope you’re spending the pounds on something special”.
Throughout this process, Chapman denied sending the messages and denied any of the sexual assaults alleged by the victim.
On the Chapman’s criminal record, the prosecution added that he was convicted of three common assaults on appeal.
In terms of commission, these matters pre-dated this case but the conviction occurred during the running of this case and also involved a female working for the defendant.
Prosecution continued that the age of the victim was an aggravating feature, arguing there was a “vulnerability” due to the “power-imbalance” between Chapman and the young student working for him.
An additional aggravating feature, they said, was that during the course of the defence, part of the defence was that the victim had “manipulated or manufactured” some of the text messages that were sent.
A defence lawyer, speaking on the pre-sentence report, noted the author deemed Chapman to be of low risk. He also noted that similar offences were contested in the County Court in respect of another complaint, with the judge substituting indecent assault charges for common assault.
He also argued a Sexual Offences Prevention Order (SOPO) was not necessary as the offending was four years ago, there has been no repetition and risk had been addressed.
District Judge Eamonn King noted the defendant was convicted on two of four original charges following a contest, which ran over a number of days, with the case adjourned for a pre-sentence report and victim impact statement to be produced.
He added the defendant “continues to deny” the charges and seeks to appeal the outcome.
District Judge King, on reading the pre-sentence report, noted the defendant “denies ever hugging or touching the individual and he denies any sexual attraction to the victim”, but pointed to a paragraph in the report which stated, “From the available evidence, it’s possible to surmise that he demonstrated risk taking and impulsive behaviour. It appears that he took advantage of his position and power in a bid to meet his sexual needs, given the victim’s young age and the fact that he was her employer”.
The report added that this demonstrated “limited victim empathy and responsibility due to his denial of the offences”.
On the victim impact statement, District Judge King described her as a young girl getting her first job, with the “world as her oyster”.
He continued: “As a result of what she says occurred, that turned on its head. It left her feeling inwardly uncomfortable, anxious and lonely. She cut herself off from her friends. She stopped going out. She didn’t want to go to school.”
He also described a “degree of manipulation” in the case, as this was the victim’s first job and there was a power imbalance between her as an employee, and Chapman as the employer.
In his sentencing remarks, District Judge King, said: “I’ve taken time to emphasise to the victim in this case that the victim did nothing wrong. The victim did everything right and the victim shouldn’t feel lonely, anxious or isolated.
“The victim should feel confident, strong and outgoing.”
Owing to the defendant’s ongoing denial of the charges, he added: “My sentencing exercise isn’t the conclusion of the case today, but I will sentence, so that we can move towards the conclusion going forward.
“I am satisfied, irrespective of what the pre-sentence report says, that the defendant took advantage of someone, attempted to groom someone and was guilty of the two offences.”
On the two counts, Chapman was sentenced to three months in prison, suspended for two years. He was also made subject to a Sexual Offences Prevention Order (SOPO) for five years and placed on the sex offenders’ register for seven years.
Following sentencing, District Judge King fixed bail for appeal at £1,000.