BRI: embracing Chinese green practices for a sustainable future
Editor's Note: This year marks the 10th anniversary of the Belt and Road Initiative (BRI) proposed by Chinese President Xi Jinping. Through the lens of foreign pundits, we take a look at 10 years of the BRI - how it achieves win-win cooperation between China and participating countries of the BRI and how it has given the people of these countries a sense of fulfillment. In an interview with Global Times (GT) reporter Li Aixin, Erik Solheim (Solheim), former under-secretary-general of the United Nations and former executive director of the UN Environment Programme, recalled how the BRI helped shorten a previously long journey in Sri Lanka to a half-hour trip. "We will all be losers in a de-globalized, de-coupled world. The BRI can play a key role in bringing the world together," Solheim said. This is the 18th piece of the series. GT: How do you evaluate the role of the BRI in promoting development in participating countries over the past 10 years? Solheim: The BRI has been a major driver of development since it was announced by President Xi Jinping in Kazakhstan 10 years ago. The China-Laos Railway has connected landlocked Laos to the Chinese and European rail network, making it possible for Laos to sell more goods and welcome more tourists. Rail corridors in Kenya and from Djibouti to Addis Ababa connect the interior of Africa to the coast, bringing opportunities for much faster development in East Africa. The Bandung-Jakarta railway in Indonesia, Hanoi metro, roads and ports in Sri Lanka - there are great examples of good south-south and BRI projects in almost every corner of the world. GT: In your experience of traveling around the world, has any BRI-related story left a deep impression on you? Solheim: Yes, many! I'll just mention two. When I was chief negotiator in the Sri Lanka peace process 15 years ago, it took a long time to travel from the airport to Colombo, the capital of Sri Lanka. When I came back last year, it took half an hour on wonderful Chinese-built highways. Traveling through Mombasa, a coastal city in Kenya, you see a lot of poverty and run down houses. Then all of a sudden, a green, clean, well-run oasis opens up. It's the end station of the Nairobi-Mombasa railway which links the capital Nairobi to the coast. The rail station stands out and is showing the future for Kenya. GT: The EU proposed the Global Gateway, and the US proposed the Build Back Better World. What do you think are the similarities and differences between these projects and the BRI? Solheim: I really wish success for the Western initiatives. What developing nations ask for is a choice of good cooperation with both China and the West. Unfortunately, up to now, a number of the Western-led initiatives have been more like media events. They lack structure, secretariat, finances and clear direction. Nearly all nations in the world want to see close people-to-people relations, investment and political cooperation with both China and the West. No one wants to choose. GT: Some people from the West are talking about "de-coupling" and "de-risking." Both seem to be another way of saying "de-globalization." Do you think "de-coupling" and "de-risking" will affect the BRI? And what role will the BRI play in maintaining globalization? Solheim: Decoupling is probably the most unwise idea in the world today. It's outright dangerous. Facing climate change, environmental degradation, economic troubles, war in Ukraine and other places, and the threat of pandemics, we need more, not less, cooperation. We will all be losers in a de-globalized, de-coupled world. The BRI can play a key role in bringing the world together. Almost all developing countries have made BRI agreements with China. As an example, when President Xi met all the leaders of Central Asia recently in Xi'an, Northwest China's Shaanxi Province, they made a very ambitious declaration on future green cooperation between China and Central Asia. GT: You have previously said that the BRI is a fantastic vehicle to promote green global development, which can boost the economy and ecology at the same time. Could you elaborate on how you think the BRI has achieved development of the economy and ecology? Solheim: In the beginning there were too many fossil fuel projects among BRI programs. In the BRI International Green Development Coalition, we argued this should stop. When President Xi pledged to stop building new coal-fired power projects overseas, it was one of the most important environmental decisions ever. Also, it happened at a time when important BRI nations like Bangladesh, Kenya and Pakistan decided they could grow their economies and go green without coal. The BRI will in the next decade become the world's most important vehicle for green energy and green transport. We will see massive investments in solar and wind power, hydrogen, electric batteries and more. GT: How do you view China's goal of achieving harmony between humanity and nature in modernization? In what way is China's story in pursuing harmony between humanity and nature relevant to other countries? Solheim: China now covers between 60 percent and 80 percent of all major green technologies in the world - solar, wind, hydro, batteries, electric cars and high-speed rail. Companies like Longi, BYD and CATL are the world leaders in their sectors. More remarkably and maybe less noticed abroad, China is also a global leader in protecting nature. It's embarking upon one of the most massive national park programs, with a focus on Qinghai Province and Xizang Autonomous Region. China is by far the biggest tree planter in the world and the global leader in desert control in Kubuqi, Inner Mongolia and other places. China has been hugely successful in the recovery of endangered species like the Giant Panda, Tibetan Antelope and Snow Leopard. A new center for mangrove restoration is being set up in Shenzhen and the fishing ban in the Yangtze will restore that magnificent ecosystem. The Belt and Road is a great opportunity for the world to learn from good Chinese green practices.
Google may bring Google Wallet for Indian users
Google Wallet can help you store your IDs, driving license, loyalty cards, concert tickets and more. You can also store your payment cards and use tap to pay to pay anywhere Google Pay is accepted. Google wallet is available in various countries but Google never launched it in India. Google let indian users stick with the Gpay which facilitates UPI payments. Tap to pay is not part of it. Also we can not store things such as IDs and Passes in indian version of Gpay. This might change and Google may launch Google Wallet in India. With the recent version of Google Wallet and Google Play Services, Google has added some flags and code which indicate that Google is working on something for Indian users regarding wallet. The first change I noticed recently when going through the Google Play Services apk was addition of two new flags Both flags are part of com.google.android.gms.pay package in the Google Play Services. This package contains all the flags for features of Gpay/Wallet. Google does server side flipping of flags to enable/disable features for users. So both these flags doesn't really provide any info about what features enabling these flags is going to bring. But the point here is that Google Wallet is not launched in India so why Google added these flags inside Play Services ? The answer could be that Google may be working on bringing Google Wallet to India. It can enable tap to pay, store payments and various other features for Indian users which we don't have in the current Gpay for India. I found similar flags in the analysis Google Wallet APK - These flags are also disabled by default. But this is again a clear indication of Google working towards something for Indian users. In both cases, enabling the flags doesn't bring anything noticeable UI or feature because there is nothing much added besides flags. Google has dogfood/testing versions internally, so the code will show up slowly in upcoming versions. The last piece of code I found is also from Google Play Services. In case you don't know, Google was working on Digilocker integration in the Google Files app which was supposed to bring your digital document inside the app such as driving license, COVID certificates, aadhar card. But Google has ditched the effort of bringing these features and they removed the "Important" tab (where digilocker was supposed to be integrated) from the Google Files app completely. So things are going to change and here is how. This is the code which I found in the Google Play Services - So the word "PASS" along with PAN, DRIVERS LICENCE, VACC CERTIFICATE & AADHAR CARD, is clear indication of the possibility of Google adding support for these directly through Google Wallet using Digilocker, just like Samsung Pass does it. This code is not old as I have checked older beta versions of Play Services where this code is not present. Here is a string which was added in a previous beta version a few weeks ago but I completely ignored it because it didn't make any sense without flags and the other code - This addition was surprising because there was nothing regarding digilocker before in the Play Services. In the words "pay_valuable", the "pay" to Wallet/Gpay and "valuable" refers to the things like Passes, loyalty cards and transit cards. Since we are talking about digilocker, these "valuable" are driving license, vaccination certificate, PAN card and Aadhar card which can be store in Google Wallet after digilocker integration. That's all about it. We will know more about it in upcoming app updates or maybe Google can itself annouce something about this.
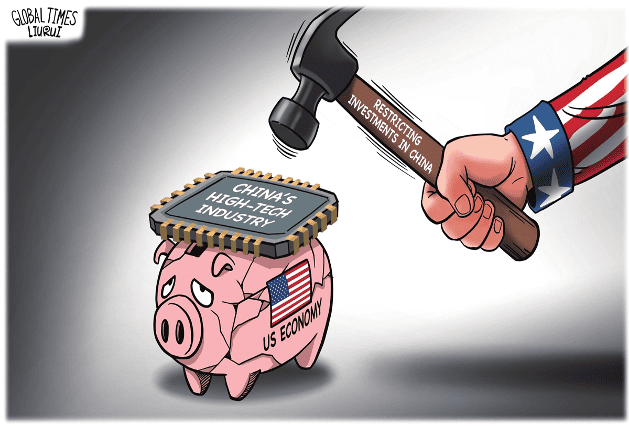
US' ban on high-tech investment cannot stifle China's high-tech development
US President Joe Biden signed an executive order on Wednesday restricting investments in China, intended to further stymie China's advances in three cutting-edge technology areas: semiconductors and microelectronics, quantum information technologies and certain artificial intelligence systems. The "decoupling" of high tech from China began under Donald Trump, and the Biden administration has continued that ambition. However, the new order doesn't target US investments already invested in China, but the new ones. The Biden administration has repeatedly claimed that the US restrictions will be narrowly targeted and will not "have a fundamental impact on affecting the investment climate for China." Biden's new executive order is still subject to consultation with the US business community and the public and is not expected to take effect until next year. The order has been brewed for a long time and has generated a lot of publicity. But almost no one believes that this executive order will deal a new practical blow to Chinese high technology, because almost everyone knows that China needs American technology more than American money. The order has gained much attention because it is seen as part of a broader trend of the US drifting away from China. The promulgation and brewing process of the executive order reflects the strong desire of American political elites to suppress China's high-tech development, as well as a fierce game between those supporting the executive order and the concerns of the technology and economic sectors about a potential backfire on the US. It is a kind of compromise. Washington obviously hopes that major allies will follow Biden's executive order. The UK's Sunak government has made cautious statements, stating that it is consulting business and the financial sector before deciding whether to follow suit. In fact, China also has the ability to influence the extent to which Biden's executive order is implemented, as well as the extent to which the US will go in terms of "decoupling" from China. We are definitely not just passive recipients of US policies. American political elites are eager to "decouple" from China as quickly and deeply as possible, but they fear two things: First, this will immediately damage the performance of relevant high-tech companies in the US, undermine their influence and further innovation. The current Biden administration, in particular, does not want to incur strong resentment from Silicon Valley and Wall Street toward the escalating "decoupling," which will ultimately lead to the loss of support for the Democratic Party. Second, they are afraid of pushing China toward more resolute independent innovation to achieve breakthroughs in key technologies such as chips. If the US "decoupling" policy gives birth to major technological achievements in China, it means that Washington will completely lose the gamble: They originally wants to stifle China's high-tech development, but ends up strangling their own companies. What China needs to do next is to fully unleash our innovation vitality, continuously reduce our dependence on high-tech products from the US, and prove that as long as we are determined to achieve independent innovation, we have the ability to accomplish things. We need to prove that being pressured by the US will only make us stronger. As long as there are several solid proofs of this trend, the US policy community will fall into unprecedented chaos, and their panic will be much more severe than when they saw the rapid expansion of the Chinese economy before Trump started the trade war. Regardless of the future of China-US relations, the current battle will be the key battle that determines the future competition between China and the US. China can only win and cannot afford to lose. High-tech products such as chips are not isolated. The innovation power of China's entire manufacturing industry and the creative vitality of the whole society are the foundation for shaping these key achievements. When pressured by the US, our society needs to generate confidence and resilience from all directions, and we need to accelerate and seize every opportunity, rather than shrink and simply defend. Otherwise, the US will gain the upper hand in momentum, and we will truly be in a passive and defensive position. We must see that the US is on the offensive, but its offensive is becoming weaker and weaker, and it is always hesitant with each step. What is presented to China are difficulties and risks, but also the dawn of victory.

The largest password leak in history exposes nearly 10 billion credentials
The largest collection of stolen passwords ever has been leaked to a notorious crime marketplace, according to cybersecurity researchers at Cybernews. This leak, dubbed RockYou2024 by its original poster “ObamaCare,” holds a file containing nearly 10 billion unique plaintext passwords. Allegedly gathered from a series of data breaches and hacks accumulated over several years, the passwords were posted on July 4th and hailed as the most extensive collection of stolen and leaked credentials ever seen on the forum. “In its essence, the RockYou2024 leak is a compilation of real-world passwords used by individuals all over the world,” the researchers told Cybernews. “Revealing that many passwords for threat actors substantially heightens the risk of credential stuffing attacks.” Credential stuffing attacks are among the most common methods criminals, ransomware affiliates, and state-sponsored hackers use to access services and systems. Threat actors could exploit the RockYou2024 password collection to conduct brute-force attacks against any unprotected system and “gain unauthorized access to various online accounts used by individuals whose passwords are included in the dataset,” the research team said. This could affect online services, cameras and hardware This could affect various targets, from online services to internet-facing cameras and industrial hardware. “Moreover, combined with other leaked databases on hacker forums and marketplaces, which, for example, contain user email addresses and other credentials, RockYou2024 can contribute to a cascade of data breaches, financial frauds, and identity thefts,” the team concluded. However, despite the seriousness of the data leak, it is important to note that RockYou2024 is primarily a compilation of previous password leaks, estimated to contain entries from a total of 4,000 massive databases of stolen credentials, covering at least two decades. This new file notably includes an earlier credentials database known as RockYou2021, which featured 8.4 billion passwords. RockYou2024 added approximately 1.5 billion passwords to the collection, spanning from 2021 through 2024, which, though a massive figure, is only a fraction of the reported 9,948,575,739 passwords in the leak. Thus, users who have changed their passwords since 2021 may not have to panic about a potential breach of their information. That said, the research team at Cybernews stressed the importance of maintaining data security. In response to the leak, they recommend immediately changing the passwords for any accounts associated with the leaked credentials, ensuring each password is strong and unique and not reused across different platforms. Additionally, they advised enabling multi-factor authentication (MFA), which requires an extra form of verification beyond the password, wherever possible, to strengthen cyber security. Lastly, tech users should utilize password manager software, which securely generates and stores complex passwords, mitigating the risk of password reuse across multiple accounts.

Coexisting and cooperating with China is the only choice for the US
US Secretary of State Antony Blinken declared at the Munich Security Conference: "If you're not at the table in the international system, you're going to be on the menu." The arrogant thinking of American political elites is evident: Whoever does not comply with the US will be excluded from the table of the American-led system and put on the menu. How arrogant. The US is actively pushing for "decoupling" from China and trying to persuade the entire West to "decouple" from China, using the term "de-risking." Washington hopes to ultimately contain China's development in order to maintain American hegemony. However, this time, Washington is facing a historically experienced and strategically rich Eastern civilization. Previous opponents targeted by the US have chosen to confront the US strategically. The US not only has the strongest technological and military capabilities but also controls global financial and information networks with a large number of allies. Those countries that had engaged in direct confrontations had suffered losses. Some of them had disintegrated, some had been weakened, and some had fallen into difficulties. However, what Washington sees from China is strategic composure and resilience. China is now staging an unprecedented and grand "Tai Chi." However, some Chinese people feel that this is not enough: Why can't we confront the US head-on? But I want to say that this is precisely the brilliance of China. This grand "Tai Chi" is about dismantling the pressure the US is putting on China. Europe is different from the US. A European diplomat once said in private that the topic of China has become toxic in the US, but in Europe, it is still possible to openly display friendliness toward China. There is genuine competition between the Europe and China despite Europe leans more toward the US between China and the US. Only in terms of ideology does the term "West" truly exist. In terms of fundamental economic interests, Europe has considerable independence. In terms of security, their attitude toward China also differs greatly from that of the US. In the Asia-Pacific region or China's periphery, the US wants to create an "Asian NATO." The specific situations of countries in dispute with China are very different. China has enormous influence in the region, is the largest trading partner of the vast majority of countries in the region and has friendly relations with most countries in the region. The disputes with countries are not fundamental strategic conflicts, and China has the ability to manage disputes with each specific country and push them to move toward neutrality to varying degrees without being tied to the US' policy toward China. China has a lot of trading partners and stakeholders in the US. The trade volume between China and the US, despite the decline, reached $664.4 billion in 2023, which shows China's huge presence in the US, and is the bond of the two countries in the current situation. The US is not a country where the political elites can have absolute say, and the huge interests have forced the US president and senior officials to repeatedly proclaim that they "don't want to decouple from China" and instead they want to "manage the US-China competition" and see "preventing a war with China" as clearly in everyone's best interest. China should engage in a "strategic battle" with the US at the closest possible distance. We need to maintain friendly relations with certain forces within the US, speed up the resumption of flights between the two countries, increase personnel exchanges and completely reverse the downturn of China-US contacts during the pandemic. In addition to the above dismantling, we also have the huge increment in the "Belt and Road." This initiative will increase China's power to compete with the US, greatly extending the front line that the US needs to maintain in containing China, making the US more powerless. In order to dismantle the US strategy toward China, China must become more diversified while maintaining strategic consistency. Our national diplomacy toward the US is very principled, rational and determined, which is clearly different from other countries targeted by the US. Our public diplomacy toward the US needs to be unique, with both "anti-American voices" and efforts to maintain friendly relations between the two societies and further expand economic and practical cooperation with the US. Just as eagles have their own way of flying and doves have their own formation, just as we see the US as complex, China must also be seen as complex in the eyes of the US. China is both a geopolitical concern and a profitable investment destination for them, and is one of the largest trading partners that is difficult to replace. Some American political elites proclaim China as an "enemy," but it is important to make the majority of Americans feel that China is not. No matter how intense the struggles between China and the US may be, we cannot shape the entire US toward an enemy direction. China has to make the US political elites recognize that it is futile to deal with China in the same way as it historically dealt with the Soviet Union and other major powers. Furthermore, willingly or unwillingly, coexistence and cooperation with China will be their only choice.